Legacy authentication has failed. By tethering your business to centralized honeypots and compromised telecom grids, you’ve inherited a terminal liability. I Am I replaces this fragility with the world’s first decentralized, zero-PII, Cookie-free, Sovereign Architecture and realtime protocol. We don't just "verify" users; we empower them to immobilize and neutralize threats in real-time.
Traditional 2FA is a "Yes/No" gate. It cannot distinguish between a loyal customer and an AitM (Adversary-in-the-Middle) attack. Whether it's SIM-swapping, SS7 exploits, or session hijacking, legacy protocols are witnesses to the crime - not guards.
OTP apps rely on a "Shared Secret." Once that secret is entered into a phishing site or intercepted via an AitM (Adversary-in-the-Middle) proxy, your defence is neutralized.
Hackers don't "break" your encryption; they "borrow" your session. By sitting between the user and the server, attackers transparently pass the OTP while stripping the session cookies for total account takeover.
The user experiences a "normal" login while a drainer bot executes in the background. The business receives a "successful" verification signal for a crime in progress.
SMS-based 2FA relies on the SS7 protocol, a 1970s telecommunications standard with zero native security. It is the most exploited authentication vector in history.
Your security budget is at the mercy of a $15-an-hour retail clerk. Through "SIM Swapping," a hacker bribes or tricks a carrier employee to port your number, instantly inheriting every recovery code tied to your identity.
SMS is a "send and pray" protocol with no environmental awareness. It cannot detect that a user is in London while their "SIM" is being accessed in Lagos.
Browsers use "Cookies" to keep users logged in. Modern "Infostealer" malware now scrapes these active session tokens directly from the user's local machine, bypassing the login screen entirely.
If a hacker steals a session token, they don't need your password or your biometric. They simply "paste" the token into their browser and they are the user. The front door remains locked, but the intruder is already inside.
Legacy MFA only checks the "Front Door" at login. It never monitors the "Hallway." Once the session is hijacked, the hacker has unrestricted, unverified access to the entire core.
Fragile OTP systems force companies to build "Account Recovery" backups. These usually rely on easily harvested email resets or static "Security Questions" mined from social media and data leaks.
Authentication is only as strong as its weakest recovery link. Attackers bypass MFA entirely by convincing support agents or bots they've "lost their phone," resetting credentials to an intruder-controlled device.
Customers are weaponized against themselves through their own "safety net." The business loses its sovereign link to the user as the hacker permanently seizes the account at the foundational level.
We offer four unique expressions of our trustless protocol. Each one delivers a zero-PII, cookie-free, and tokenized defence that acts like an "Active Peripheral Reflex." For the first time, customers now have complete sovereignty and guardianship over their accounts and assets.
The I Am I authentication framework offers no passcodes, no SMS text message, nor simplified Yes/No interfaces. Optimizing realtime push technologies, we’ve finally bridged the gap between technology and the human instinct to protect whats yours. This truly is a first for real realtime empowerment.
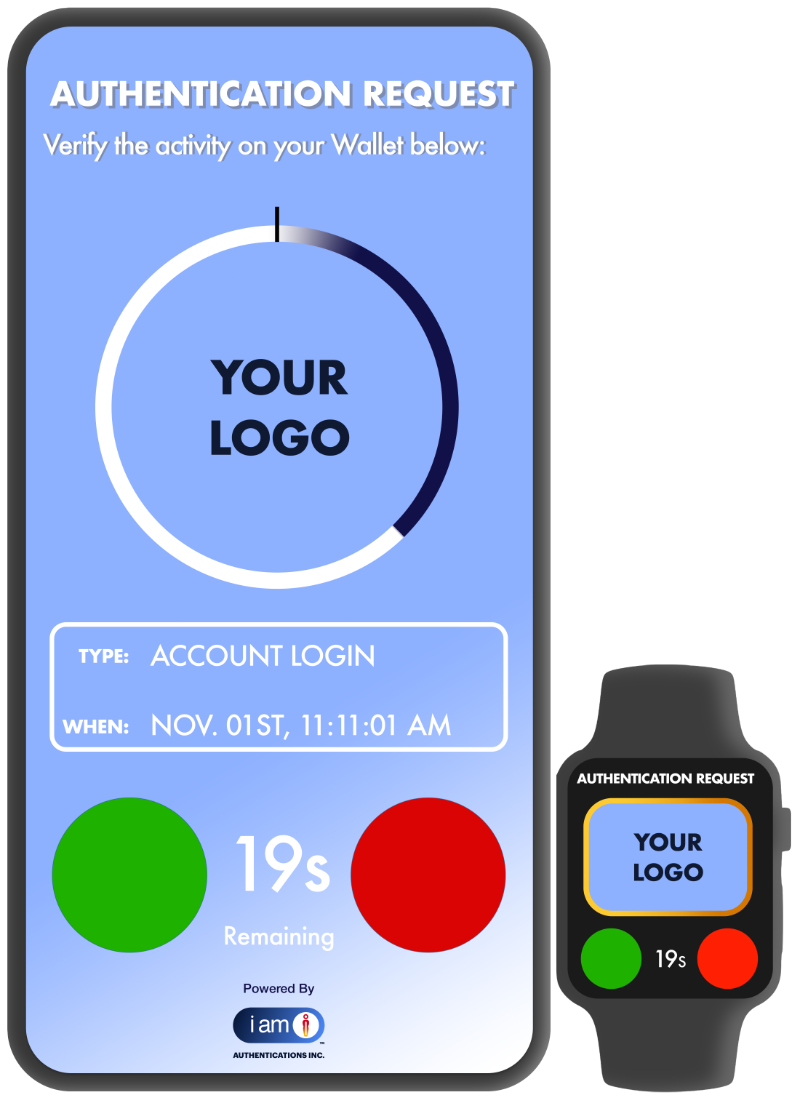
This is the "Command" pillar. While legacy "Approve/Deny" notifications are passive and binary, I Am I Sovereign Push transforms the notification into a forensic dashboard. It moves the user from a mindless "tap" to a thoroughly informed decision-maker.
Every push is an t, out-of-band communication that bypasses the telco grid. It delivers Contextual Intelligence for the user to see precise activity details involving their account(s) and assets. Most importantly, it includes the Kill-Switch: a "Report & Immobilize" button that doesn't just deny the request but alerts the business to a live threat in real-time.
We eliminate "MFA Fatigue" by requiring a cognitive handshake. The user is empowered to act as a peripheral security guard for the business. If a hacker triggers a request, the user identifies it, kills the session, and secures their account - all within a few seconds.
Built for speed and conversion. It replaces high-friction passwords and codes with a seamless, tokenized exchange between the user’s trusted device and your core infrastructure.
Unlike cloud-synced passkeys, this is a unique, non-syncable tokenization value. By leveraging the device’s Secure Enclave, it signs cryptographic challenges that are impossible to phish, proxy, or spoof.
Users experience zero-friction entry while the business achieves absolute cryptographic certainty. By eliminating the need for password vaults, you liquidate the honeypot and permanently shrink your network’s attack surface.

This is the "Privacy" pillar. Most biometric systems (FaceID/TouchID) are binary—they just tell the app "Yes/No." I Am I goes further by wrapping that biometric check in a Zero-PII protocol.
We never see, touch, or store the user’s biometric data. The "Match" happens locally at the edge. I Am I then generates a one-time forensic token that proves the match occurred without ever exposing the user's biological data to a central honeypot.
Absolute immunity from biometric data breaches. Even if I Am I or the Client were "hacked," there is no biometric database to steal. Identity remains sovereign to the user.

This is the "High-Stakes" pillar. It combines the tokenization strength of Passwordless with the human intent of Biometrics. It is the ultimate defence against "mindless" authentication and automated bot attacks.
It requires a "Verified Action." The system checks for the Device Token + Local Biometric + Real-time Intent. This creates a "Three-Key" lock that ensures a human is consciously authorizing the specific transaction in that specific moment.
Total immobilization of remote attacks. Even if a hacker has the user's phone, they cannot bypass the biometric. Even if they have a biometric spoof, they don't have the hardware token. It is the "Active Peripheral Reflex" in its most potent form.

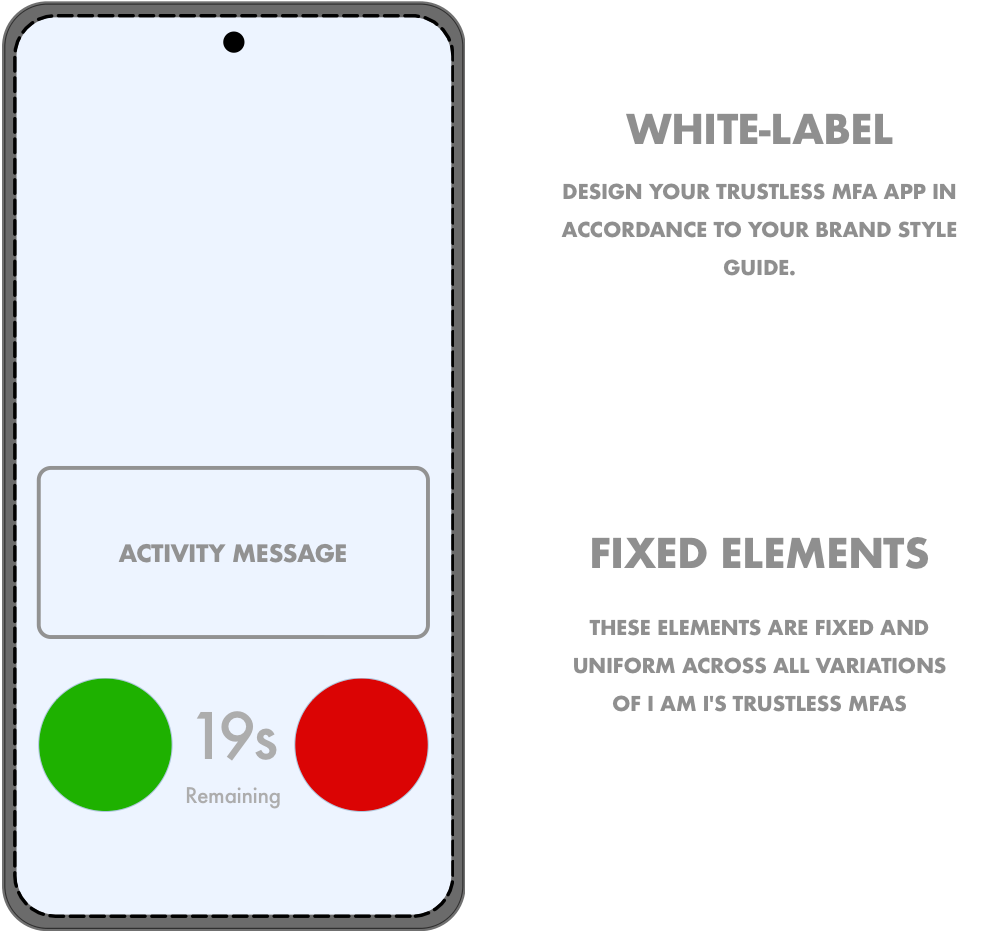
The engine is ours. The experience, loyalty, and relationship remain yours.
Legacy 2FAs/MFAs fracture the user journey by outsourcing trust. I Am I removes this friction with a white-labeled framework that keeps your brand at the center of every interaction. As the steward of your customers' safety, you bridge and transform security from a technical hurdle into a reinforcement of your brand relationship.
Owning the experience turns protection into a strategic asset. Positioning your business as the architect of future-state security drives deep-seated loyalty and revenue. Every "Sovereign Handshake" becomes a brand-building moment that credits your company and not a vendor with your customers' peace of mind.
Institutional Stewardship: Position your organization as a leader in privacy by delivering advanced, Cookie-free, Zero-PII protection directly under your own brand identity.
Elevated Customer Lifetime Value: Drive loyalty by providing a unique, empowering account security experiences that competitors cannot replicate.
Strategic Ownership: Retain absolute control over the customer journey, ensuring your brand, and not vendors, get credited for your customers' peace of mind.
Frictionless Trust: Simplify the user experience with a seamless, intuitive interface that feels like a natural extension of your existing digital ecosystem.

In the consumer world, friction is the enemy of growth. But legacy security is nothing but friction. I Am I transforms authentication from a "barrier" into a Digital Reflex. By deploying a protocol that requires no passwords, no syncable keys, and zero PII, you aren't just protecting your users, you are liberating them.
For the business, this is the ultimate de-risking event. By liquidating the centralized honeypots of passwords and PII, you remove the liability that keeps CEOs and Founders awake. No data trails, no cookies, and no cryptographic secrets for Quantum computers to harvest.
You don't just secure the data; you eliminate the need to hold it.
I Am I is engineered to vanish into your existing ecosystem or stand alone as your primary security gateway. We provide the infrastructure of immunity without the development lag or the burden of maintaining vulnerable password vaults. Whether you are scaling a startup or hardening an enterprise, IAmI removes the "centralized honeypot" liability from your roadmap on Day 1.
Seamlessly embed our non-cryptographic, tokenized protocol directly into your existing mobile app. You maintain 100% UI/UX control while offloading the entire authentication security logic to IAmI’s backend "Reflex" architecture. No keys to manage, no secrets to store, and no cryptographic overhead.
No mobile app? No problem. We engineer and deploy a dedicated, white-label security container tailored to your brand. This is a forensic-grade, standalone gateway that serves as your customers' central command for identity. It’s not a template; it’s a custom-built fortress that gives you an immediate, hardened mobile presence.
Digital threats evolve by the second. We should connect to discuss how you can immediately fortify your customers’ accounts and safeguard their assets.
Whether you're ready to deploy or simply looking to explore the future of non-refutable security, let’s start a discovery session to secure your ecosystem before the next breach.
Reach out for "your" next-gen authentication service: IAmI Trustless MFA